Introducing EVMD — Our EVM Bytecode Decompiler
We're releasing EVMD v2.0.0 beta, a free EVM bytecode decompiler with raw and AI-enhanced decompilation, function signature extraction, and a clean dark-mode interface.

Why We Built EVMD
If you've ever tried to reverse-engineer a contract on-chain, you know the pain. Most EVM decompilers are either paywalled, abandoned, half-broken, or require local toolchain setup that nobody has time for.
We wanted something better, something fast, free, and actually useful , so we built EVMD.
EVMD is a web-based EVM bytecode decompiler. Paste bytecode, hit Decompile, get readable Solidity-like output. No setup, no API keys, no wallet connect, no cost. Just works.
How It Works
Under the hood, EVMD is powered by heimdall-rs, a battle-tested open-source decompiler that traces EVM opcodes directly from bytecode and reconstructs Solidity-like code.
The decompilation pipeline:
- Bytecode parsing — Raw EVM bytecode is disassembled into opcodes
- Control flow recovery — Jump targets and basic blocks are reconstructed
- Function boundary detection — Function selectors are matched against known signature databases
- Solidity reconstruction — Opcodes are lifted into readable Solidity-like output
Raw Decompiled Output
The raw decompiler output gives you the full contract structure, state variables, events, function signatures, and reconstructed logic. It won't always compile, but the logic should be clear.
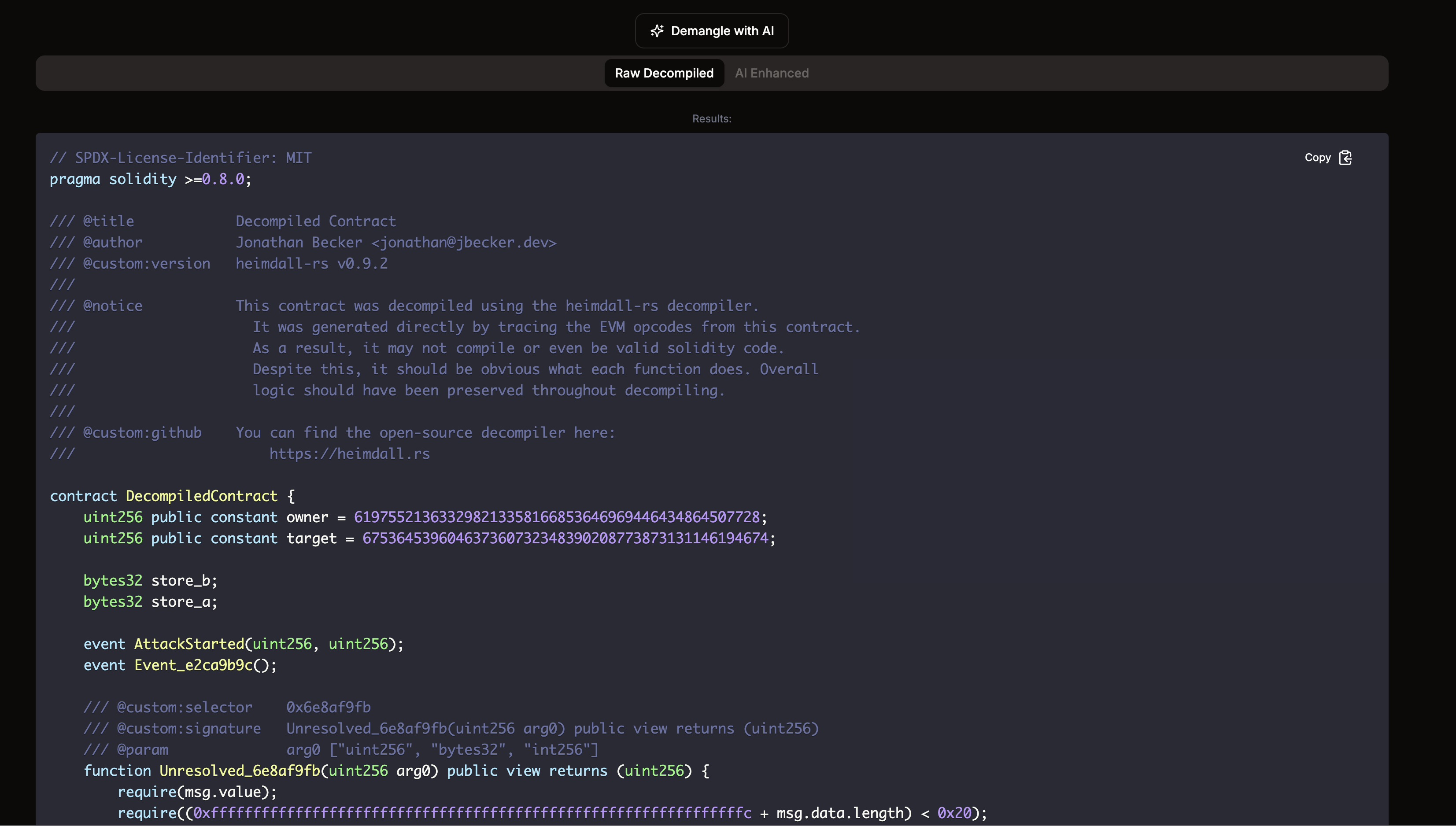
You get proper annotations including the SPDX license identifier, author credits, heimdall version, and a direct link to the open-source decompiler.
Function Signatures
EVMD extracts and displays all function signatures with their selectors, parameter types, mutability, and resolved names when available.
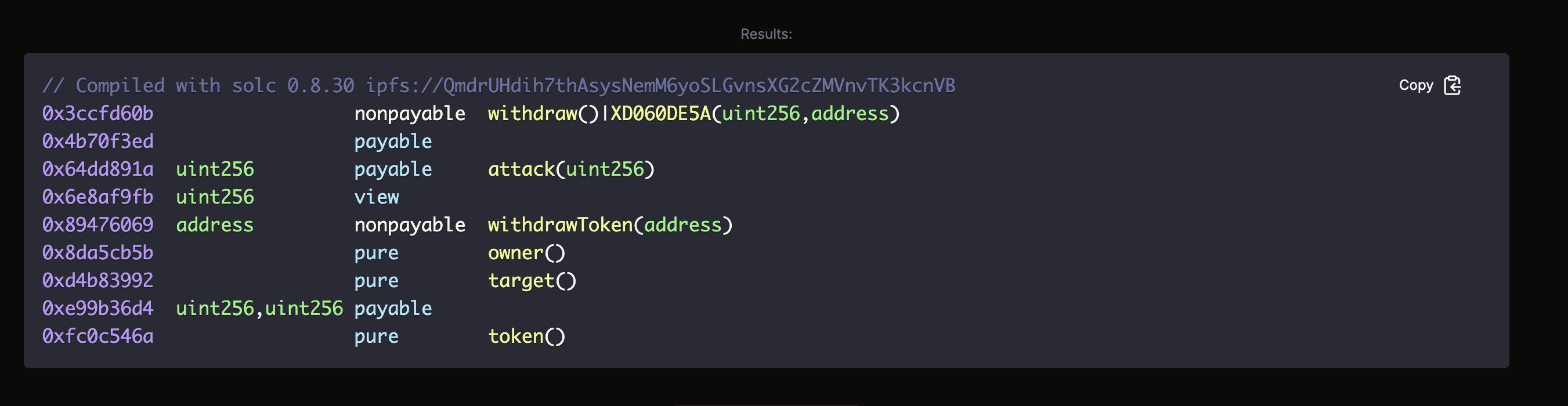
This makes it easy to quickly understand a contract's external interface — what functions it exposes, whether they're payable, and what they're called.
AI-Enhanced Demangling
This is where EVMD stands apart from every other decompiler out there.
Raw decompiled output is functional but ugly — variables are named store_a, events are Event_e2ca9b9c, and function names are Unresolved_6e8af9fb. Good luck reading that during an incident.
Hit "Demangle with AI" and our proprietary DarkGrove AI agent rewrites the output with meaningful, context-aware names:
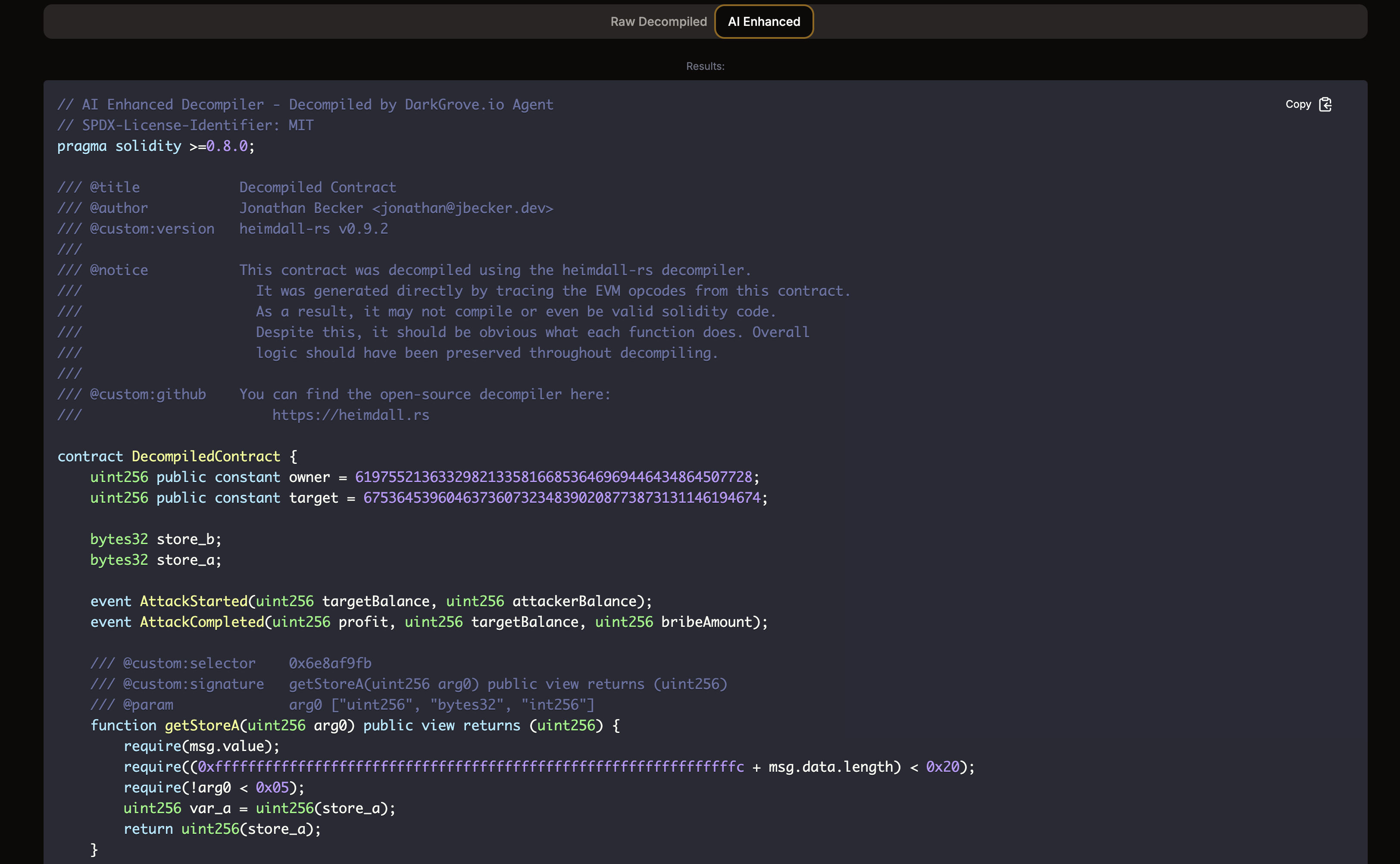
The AI Enhanced mode:
- Renames storage variables to contextual names
- Resolves event signatures (e.g.,
AttackStarted(targetBalance, attackerBalance)instead ofAttackStarted(uint256, uint256)) - Improves function names based on their logic (e.g.,
getStoreAinstead ofUnresolved_6e8af9fb) - Preserves all original annotations and structure
The raw and AI-enhanced outputs are side by side, toggle between tabs to compare.
Try It Now
EVMD v2.0.0 beta is live and completely free at decompiler.darkgrove.io.
Whether you're an auditor investigating a suspicious contract, a researcher studying DeFi protocols, or a developer debugging deployed bytecode, EVMD gets you from raw hex to readable Solidity in seconds.
We're actively improving the AI enhancement layer and adding support for more contract patterns. This is just the beginning.
Follow @darkgroveio for updates. Built by DarkGrove Labs.